Apple released macOS 11 Big Sur on November 12th, 2020. While the operating system upgrade is currently available, do not upgrade unless all of your music production devices and software are officially deemed compatible by their respective manufacturers. Check the Manufacturer Compatibility List.
macOS Big Sur is coming in the fall of 2020, so this is a good time to learn how to create a macOS Big Sur bootable USB so you can install it on multiple Macs. This article shows you how to create the macOS installer on Windows 10 using UUByte DMG Editor, which is a professional and cross-platform disk authoring tool.
How to Download macOS Big Sur DMG File
- Tested on production 1.4GHz quad-core Intel Core i5-based 13-inch MacBook Pro systems with 8GB RAM, 256GB SSD, and prerelease macOS Big Sur. Tested with prerelease Safari 14.0.1 and Chrome v85.0.4183.121. Performance will vary based on usage, system configuration, network connection,.
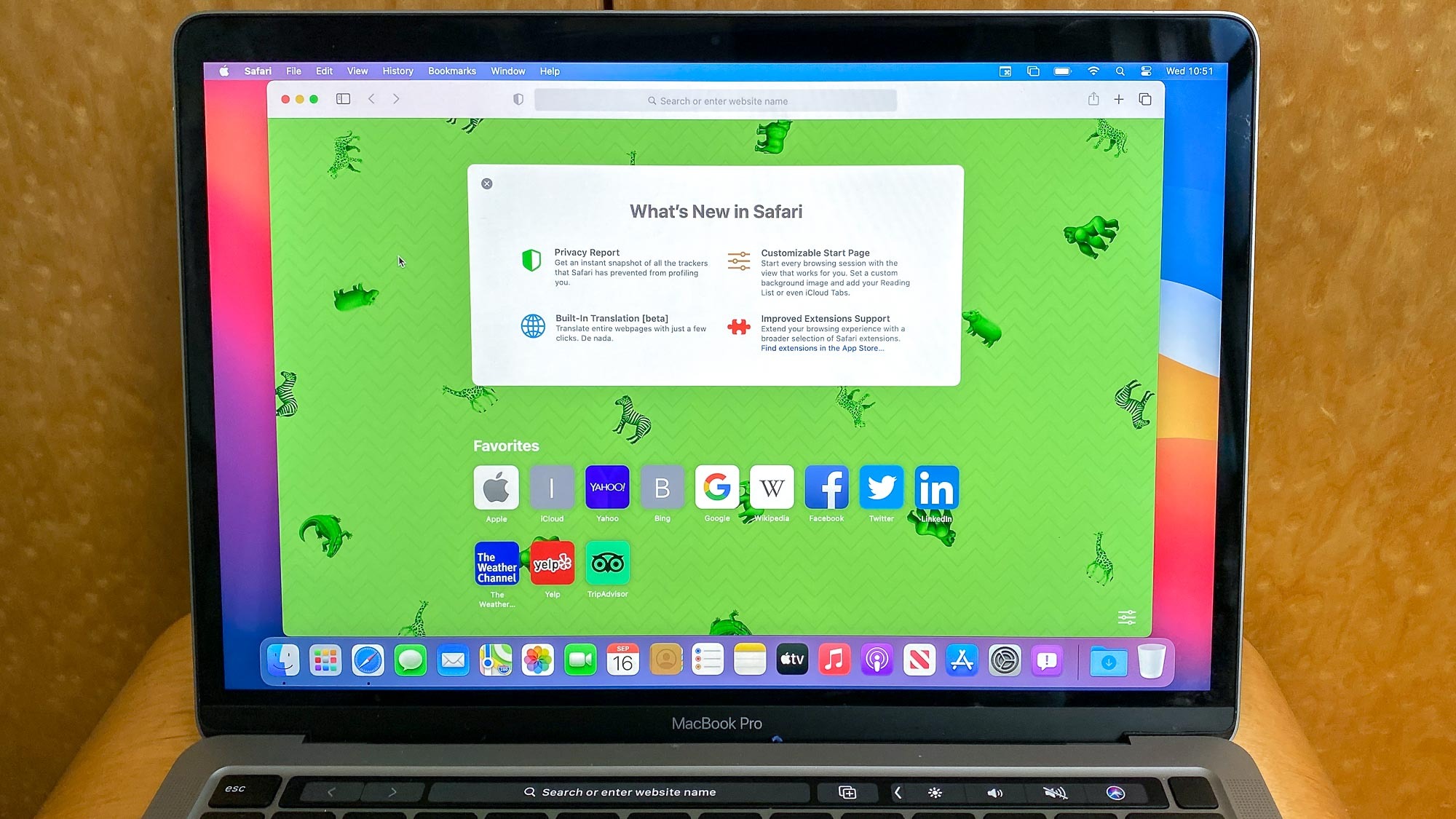
- MacOS Big Sur, the latest version of the world’s most advanced desktop operating system, is now available to Mac users as a free software update. Big Sur introduces a beautiful redesign and is packed with new enhancements for key apps including Safari, Messages, and Maps, as well as new privacy features. And Big Sur has been engineered, down.
- Apple’s Big Sur OS update is now available for download for all Mac users, but what does version 11 of macOS actually offer, and how can you take advantage of the new features?Rather than.
Let's briefly look at how to download macOS Big Sur DMG file. Of course, there are several third-party sources that are now offering the macOS Big Sur beta version as DMG but not all of them are trustworthy. For that reason, we recommend that you sign up for the Apple Beta Software Program here and proceed to register an Apple device so you can get access to download the OS profile and Big Sur Install app. Obviously, you can't register your Windows 10 computer so you will need a Mac computer to acquire the app.
If you don't have a Mac at hand, then you can directly download macOS Big DMG file via (link 1 or link2). The download might be a little slow as it is hosted on a third-party website. It could be much faster if it were hosted on Apple server or Google Drive.
Create a macOS Big Sur Bootable USB on Windows 10 PC
After downloading macOS Big Sur DMG file, you have to burn macOS dmg file to an USB. For this stage of the process, we will use UUByte DMG Editor, a professional disk authoring and disk image management tool. It is one of the simplest yet most powerful tools for managing DMG and other disk image file formats and is available for both Windows and Mac.
The interface and functions are easy to understand and even first-time users with no experience working with DMG files can easily get up to speed with the software in a few minutes. Once you have the DMG file on your PC, proceed with the following steps to create a bootable USB installer for macOS Big Sur beta.
Step 1: Download and install UUByte DMG Editor on Windows 10 using the official ISO installation file, which you can download from the UUByte website here.
Step 2: Insert the USB drive into an available port on Windows 10 PC and launch UUByte DMG Editor. Select the 'Burn' option on the welcome page.
Step 3: Select the DMG file using File Explorer and click 'Browse' button to 'import macOS Big Sur dmg file into the software. Make sure the correct drive (USB) is selected in the appropriate section.
Step 4: Name the USB Drive volume label as 'Big Sur Installer' or something similar, then click on 'Burn' tab to format the drive and create a bootable macOS Big Sur USB installer.
Step 5: Wait about 15 minutes and you will see the completion message on the screen. This means a bootable USB installer is ready and you can use that USB to install macOS on target computer.
Creating macOS Big Sur install USB on Windows 10 is simple with the help of UUByte DMG Editor. It is one of the best tools for managing DMG file on a Windows PC.
Troubleshooting when Burning macOS DMG to USB
Occasionally, you may run into some errors while preparing to burn macOS DMG to a USB drive. Here is a list of the most common problems and how to fix them:
USB Drive Not Detected: If your USB stick isn't being detected, it's a system problem or an issue with the drive itself. Make sure USB drive is installed on the PC. You can also try another drive to see if it works, or switch it to a different port.
Insufficient Space: This is another common problem that's easily rectified. All you need to do is use a different flash drive with additional capacity. macOS Big Sur disk image files usually require about 16GB capacity on the USB drive.
Corrupted DMG File: In this case, you can either try to repair the corrupted file if you have the knowledge to do so, or go ahead and download the file again from Apple's servers via the Beta Program. This issue sometimes occurs when you get disk images from third-party websites, which is why we recommend the Beta Program.
USB Installer Not Working: In rare cases, the burning process might have had an error. If so, you can use UUByte DMG Editor to burn the DMG file again to the USB drive. However, make sure that there's no issue with the DMG file itself because the editor has a high burning accuracy rate and such problems should not occur frequently.
Conclusion
Once you have macOS Big Sur installer USB ready, you can insert it into any Mac and run the program to install Apple's latest desktop operating system. Big Sur is officially coming in the fall and has a ton of updated features on nearly all fronts, including the OS interface, Safari, Siri, Messages for desktop, etc. But you should also know that since the currently available DMG is only a public beta tester version, it is bound to have bugs and other issues. If you're on the beta program, you can use the feedback app to let Apple know what the issue is. Unfortunately, that also means that there's nothing you can do about it if you're not on the beta program.
About Apple security updates
For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
Apple security documents reference vulnerabilities by CVE-ID when possible.
For more information about security, see the Apple Product Security page.
macOS Big Sur 11.4
Released May 24, 2021
AMD
Available for: macOS Big Sur
Impact: A remote attacker may be able to cause unexpected application termination or arbitrary code execution
Description: A logic issue was addressed with improved state management.
CVE-2021-30678: Yu Wang of Didi Research America
AMD
Available for: macOS Big Sur
Impact: A local user may be able to cause unexpected system termination or read kernel memory
Description: A logic issue was addressed with improved state management.
CVE-2021-30676: shrek_wzw
App Store
Available for: macOS Big Sur
Impact: A malicious application may be able to break out of its sandbox
Description: A path handling issue was addressed with improved validation.
CVE-2021-30688: Thijs Alkemade of Computest Research Division
AppleScript
Available for: macOS Big Sur
Impact: A malicious application may bypass Gatekeeper checks
Description: A logic issue was addressed with improved state management.
CVE-2021-30669: Yair Hoffman
Audio
Available for: macOS Big Sur
Impact: Processing a maliciously crafted audio file may lead to arbitrary code execution
Description: This issue was addressed with improved checks.
CVE-2021-30707: hjy79425575 working with Trend Micro Zero Day Initiative
Audio
Available for: macOS Big Sur
Impact: Parsing a maliciously crafted audio file may lead to disclosure of user information
Description: This issue was addressed with improved checks.
CVE-2021-30685: Mickey Jin (@patch1t) of Trend Micro
Core Services
Available for: macOS Big Sur
Impact: A malicious application may be able to gain root privileges
Description: A validation issue existed in the handling of symlinks. This issue was addressed with improved validation of symlinks.
CVE-2021-30681: Zhongcheng Li (CK01)
CoreAudio
Available for: macOS Big Sur
Impact: Processing a maliciously crafted audio file may disclose restricted memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2021-30686: Mickey Jin of Trend Micro
Crash Reporter
Available for: macOS Big Sur
Impact: A malicious application may be able to modify protected parts of the file system
Description: A logic issue was addressed with improved state management.
CVE-2021-30727: Cees Elzinga
CVMS
Available for: macOS Big Sur
Impact: A local attacker may be able to elevate their privileges
Description: This issue was addressed with improved checks.
Big Sur Osx
CVE-2021-30724: Mickey Jin (@patch1t) of Trend Micro
Dock
Available for: macOS Big Sur
Impact: A malicious application may be able to access a user's call history
Description: An access issue was addressed with improved access restrictions.
CVE-2021-30673: Josh Parnham (@joshparnham)
Graphics Drivers
Available for: macOS Big Sur
Impact: A remote attacker may cause an unexpected application termination or arbitrary code execution
Description: A logic issue was addressed with improved state management.
CVE-2021-30684: Liu Long of Ant Security Light-Year Lab
Graphics Drivers
Available for: macOS Big Sur
Impact: A malicious application may be able to execute arbitrary code with kernel privileges
Description: An out-of-bounds write issue was addressed with improved bounds checking.
CVE-2021-30735: Jack Dates of RET2 Systems, Inc. (@ret2systems) working with Trend Micro Zero Day Initiative
Heimdal
Available for: macOS Big Sur
Impact: A local user may be able to leak sensitive user information
Description: A logic issue was addressed with improved state management.
CVE-2021-30697: Gabe Kirkpatrick (@gabe_k)
Heimdal

Available for: macOS Big Sur
Impact: A malicious application may cause a denial of service or potentially disclose memory contents
Description: A memory corruption issue was addressed with improved state management.
CVE-2021-30710: Gabe Kirkpatrick (@gabe_k)
Heimdal
Available for: macOS Big Sur
Impact: A malicious application could execute arbitrary code leading to compromise of user information
Description: A use after free issue was addressed with improved memory management.
CVE-2021-30683: Gabe Kirkpatrick (@gabe_k)
ImageIO
Available for: macOS Big Sur
Impact: Processing a maliciously crafted image may lead to disclosure of user information
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2021-30687: Hou JingYi (@hjy79425575) of Qihoo 360
ImageIO
Available for: macOS Big Sur
Impact: Processing a maliciously crafted image may lead to disclosure of user information
Description: This issue was addressed with improved checks.
CVE-2021-30700: Ye Zhang(@co0py_Cat) of Baidu Security
ImageIO
Available for: macOS Big Sur
Impact: Processing a maliciously crafted image may lead to arbitrary code execution
Description: This issue was addressed with improved checks.
CVE-2021-30701: Mickey Jin (@patch1t) of Trend Micro and Ye Zhang of Baidu Security
ImageIO
Available for: macOS Big Sur
Impact: Processing a maliciously crafted ASTC file may disclose memory contents
Description: This issue was addressed with improved checks.
CVE-2021-30705: Ye Zhang of Baidu Security
Intel Graphics Driver
Available for: macOS Big Sur
Impact: A local user may be able to cause unexpected system termination or read kernel memory
Description: An out-of-bounds read issue was addressed by removing the vulnerable code.
CVE-2021-30719: an anonymous researcher working with Trend Micro Zero Day Initiative
Intel Graphics Driver
Available for: macOS Big Sur
Impact: A malicious application may be able to execute arbitrary code with kernel privileges
Description: An out-of-bounds write issue was addressed with improved bounds checking.
CVE-2021-30728: Liu Long of Ant Security Light-Year Lab
CVE-2021-30726: Yinyi Wu(@3ndy1) of Qihoo 360 Vulcan Team
Kernel
Available for: macOS Big Sur
Impact: A malicious application may be able to execute arbitrary code with kernel privileges
Description: A logic issue was addressed with improved validation.
CVE-2021-30740: Linus Henze (pinauten.de)
Kernel
Available for: macOS Big Sur
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A logic issue was addressed with improved state management.
CVE-2021-30704: an anonymous researcher
Kernel
Available for: macOS Big Sur
Impact: Processing a maliciously crafted message may lead to a denial of service
Description: A logic issue was addressed with improved state management.
CVE-2021-30715: The UK's National Cyber Security Centre (NCSC)
Kernel
Available for: macOS Big Sur
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A buffer overflow was addressed with improved size validation.
CVE-2021-30736: Ian Beer of Google Project Zero
Kernel
Available for: macOS Big Sur
Impact: A local attacker may be able to elevate their privileges
Description: A memory corruption issue was addressed with improved validation.
CVE-2021-30739: Zuozhi Fan (@pattern_F_) of Ant Group Tianqiong Security Lab
Kext Management
Available for: macOS Big Sur
Impact: A local user may be able to load unsigned kernel extensions
Description: A logic issue was addressed with improved state management.
CVE-2021-30680: Csaba Fitzl (@theevilbit) of Offensive Security
LaunchServices
Available for: macOS Big Sur
Impact: A malicious application may be able to break out of its sandbox
Description: This issue was addressed with improved environment sanitization.
CVE-2021-30677: Ron Waisberg (@epsilan)
Login Window
Available for: macOS Big Sur
Impact: A person with physical access to a Mac may be able to bypass Login Window
Description: A logic issue was addressed with improved state management.
CVE-2021-30702: Jewel Lambert of Original Spin, LLC.
Available for: macOS Big Sur
Impact: An attacker in a privileged network position may be able to misrepresent application state
Description: A logic issue was addressed with improved state management.
CVE-2021-30696: Fabian Ising and Damian Poddebniak of Münster University of Applied Sciences
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted USD file may disclose memory contents
Description: An information disclosure issue was addressed with improved state management.
CVE-2021-30723: Mickey Jin (@patch1t) of Trend Micro
CVE-2021-30691: Mickey Jin (@patch1t) of Trend Micro
CVE-2021-30692: Mickey Jin (@patch1t) of Trend Micro
CVE-2021-30694: Mickey Jin (@patch1t) of Trend Micro
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted USD file may lead to unexpected application termination or arbitrary code execution
Description: A memory corruption issue was addressed with improved state management.
CVE-2021-30725: Mickey Jin (@patch1t) of Trend Micro
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted USD file may disclose memory contents
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2021-30746: Mickey Jin (@patch1t) of Trend Micro
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted image may lead to arbitrary code execution
Description: A validation issue was addressed with improved logic.
Big Sur Os Review
CVE-2021-30693: Mickey Jin (@patch1t) & Junzhi Lu (@pwn0rz) of Trend Micro
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted USD file may disclose memory contents
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2021-30695: Mickey Jin (@patch1t) & Junzhi Lu (@pwn0rz) of Trend Micro
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted USD file may lead to unexpected application termination or arbitrary code execution
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2021-30708: Mickey Jin (@patch1t) & Junzhi Lu (@pwn0rz) of Trend Micro
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted USD file may disclose memory contents
Description: This issue was addressed with improved checks.
CVE-2021-30709: Mickey Jin (@patch1t) of Trend Micro
NSOpenPanel
Available for: macOS Big Sur
Impact: An application may be able to gain elevated privileges
Big Sur Os Review
Description: This issue was addressed by removing the vulnerable code.
CVE-2021-30679: Gabe Kirkpatrick (@gabe_k)
OpenLDAP
Available for: macOS Big Sur
Impact: A remote attacker may be able to cause a denial of service
Description: This issue was addressed with improved checks.
CVE-2020-36226
CVE-2020-36227
CVE-2020-36223
CVE-2020-36224
CVE-2020-36225
CVE-2020-36221
CVE-2020-36228
CVE-2020-36222
CVE-2020-36230
CVE-2020-36229
PackageKit
Available for: macOS Big Sur
Impact: A malicious application may be able to overwrite arbitrary files
Description: An issue with path validation logic for hardlinks was addressed with improved path sanitization.
CVE-2021-30738: Qingyang Chen of Topsec Alpha Team and Csaba Fitzl (@theevilbit) of Offensive Security
Security
Available for: macOS Big Sur
Impact: Processing a maliciously crafted certificate may lead to arbitrary code execution
Description: A memory corruption issue in the ASN.1 decoder was addressed by removing the vulnerable code.
CVE-2021-30737: xerub
smbx
Available for: macOS Big Sur
Impact: An attacker in a privileged network position may be able to perform denial of service
Description: A logic issue was addressed with improved state management.
CVE-2021-30716: Aleksandar Nikolic of Cisco Talos
smbx
Available for: macOS Big Sur
Impact: An attacker in a privileged network position may be able to execute arbitrary code
Description: A memory corruption issue was addressed with improved state management.
CVE-2021-30717: Aleksandar Nikolic of Cisco Talos
smbx
Available for: macOS Big Sur
Impact: An attacker in a privileged network position may be able to leak sensitive user information
Description: A path handling issue was addressed with improved validation.
CVE-2021-30721: Aleksandar Nikolic of Cisco Talos
smbx
Available for: macOS Big Sur
Impact: An attacker in a privileged network position may be able to leak sensitive user information
Description: An information disclosure issue was addressed with improved state management.
CVE-2021-30722: Aleksandar Nikolic of Cisco Talos
smbx
Available for: macOS Big Sur
Impact: A remote attacker may be able to cause unexpected application termination or arbitrary code execution
Big Sur Os Wallpaper

Description: A logic issue was addressed with improved state management.
CVE-2021-30712: Aleksandar Nikolic of Cisco Talos
Software Update
Available for: macOS Big Sur
Impact: A person with physical access to a Mac may be able to bypass Login Window during a software update
Description: This issue was addressed with improved checks.
CVE-2021-30668: Syrus Kimiagar and Danilo Paffi Monteiro
SoftwareUpdate
Available for: macOS Big Sur
Impact: A non-privileged user may be able to modify restricted settings
Description: This issue was addressed with improved checks.
CVE-2021-30718: SiQian Wei of ByteDance Security
TCC
Available for: macOS Big Sur
Impact: A malicious application may be able to send unauthorized Apple events to Finder
Description: A validation issue was addressed with improved logic.
CVE-2021-30671: Ryan Bell (@iRyanBell)
TCC
Available for: macOS Big Sur
Impact: A malicious application may be able to bypass Privacy preferences. Apple is aware of a report that this issue may have been actively exploited.
Description: A permissions issue was addressed with improved validation.
CVE-2021-30713: an anonymous researcher
WebKit
Available for: macOS Big Sur
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A cross-origin issue with iframe elements was addressed with improved tracking of security origins.
CVE-2021-30744: Dan Hite of jsontop
WebKit
Available for: macOS Big Sur
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: A use after free issue was addressed with improved memory management.
CVE-2021-21779: Marcin Towalski of Cisco Talos
WebKit
Available for: macOS Big Sur
Impact: A malicious application may be able to leak sensitive user information
Description: A logic issue was addressed with improved restrictions.
CVE-2021-30682: an anonymous researcher and 1lastBr3ath
WebKit
Available for: macOS Big Sur
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A logic issue was addressed with improved state management.
CVE-2021-30689: an anonymous researcher
WebKit
Available for: macOS Big Sur
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2021-30749: an anonymous researcher and mipu94 of SEFCOM lab, ASU. working with Trend Micro Zero Day Initiative
CVE-2021-30734: Jack Dates of RET2 Systems, Inc. (@ret2systems) working with Trend Micro Zero Day Initiative
WebKit
Available for: macOS Big Sur
Impact: A malicious website may be able to access restricted ports on arbitrary servers
Description: A logic issue was addressed with improved restrictions.
CVE-2021-30720: David Schütz (@xdavidhu)
WebRTC
Available for: macOS Big Sur
Impact: A remote attacker may be able to cause a denial of service
Description: A null pointer dereference was addressed with improved input validation.
CVE-2021-23841: Tavis Ormandy of Google
CVE-2021-30698: Tavis Ormandy of Google
Additional recognition
App Store
We would like to acknowledge Thijs Alkemade of Computest Research Division for their assistance.
CoreCapture
We would like to acknowledge Zuozhi Fan (@pattern_F_) of Ant-financial TianQiong Security Lab for their assistance.
ImageIO
We would like to acknowledge Jzhu working with Trend Micro Zero Day Initiative and an anonymous researcher for their assistance.
Mail Drafts
We would like to acknowledge Lauritz Holtmann (@_lauritz_) for their assistance.
WebKit
We would like to acknowledge Chris Salls (@salls) of Makai Security for their assistance.
Comments are closed.